Access Management , Encryption & Key Management , Identity & Access Management
Exposing The Misuse of The Foundation of Online Security

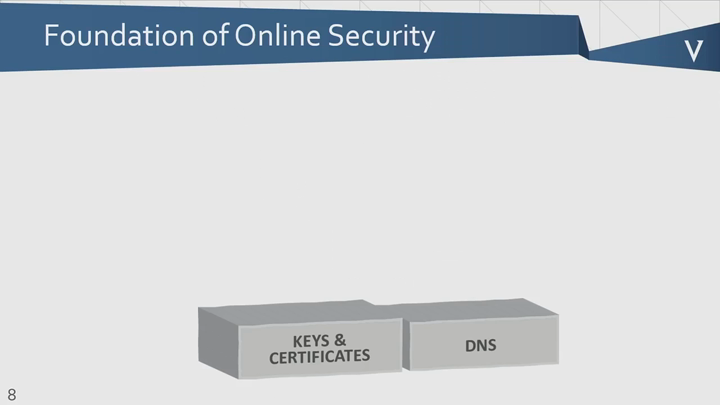
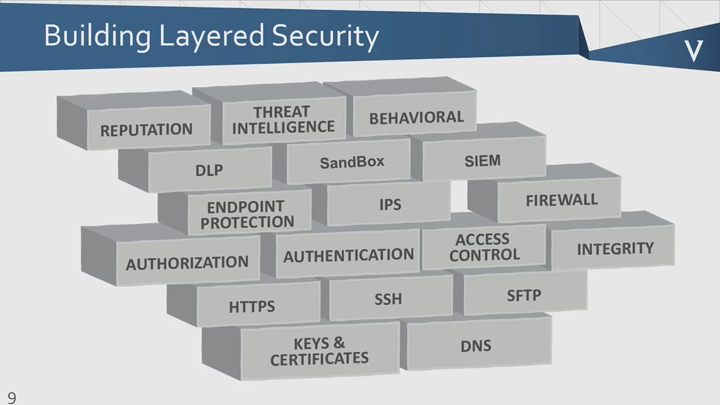
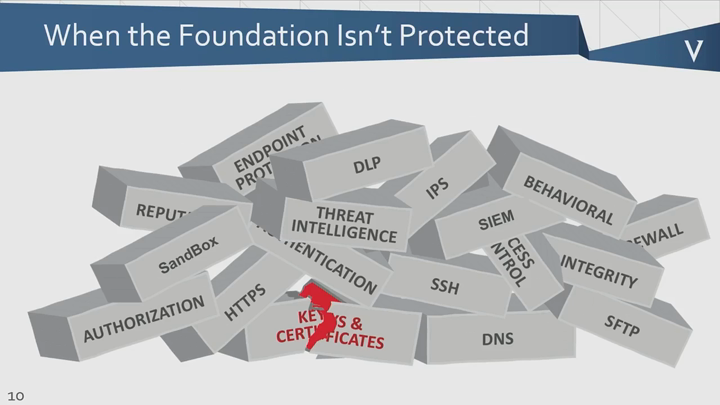
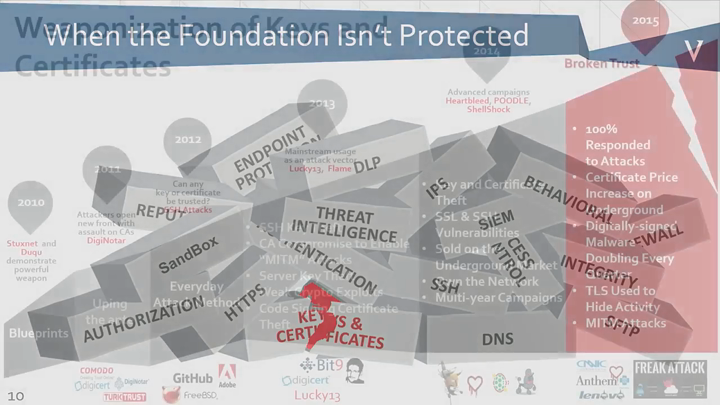
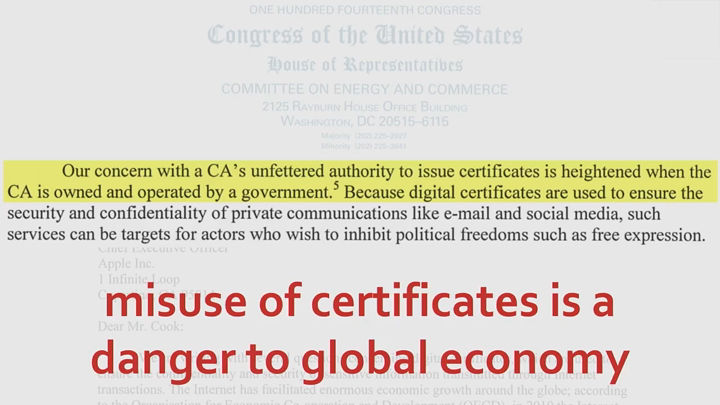
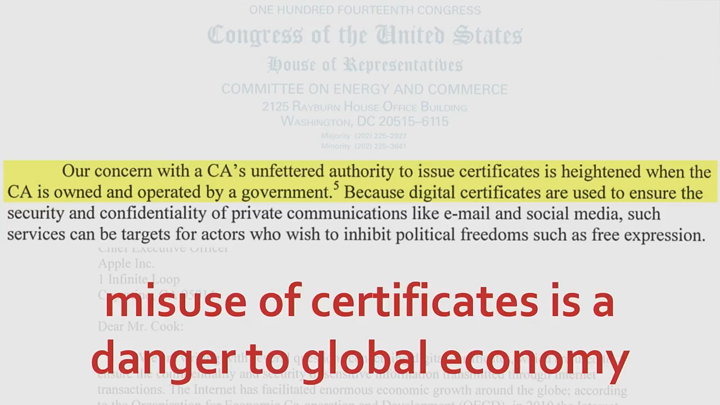
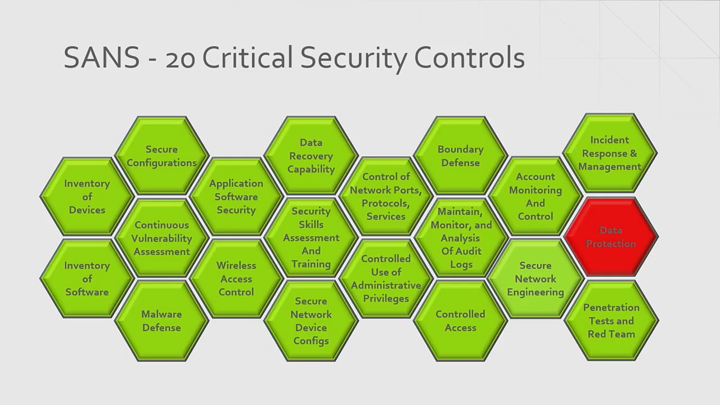
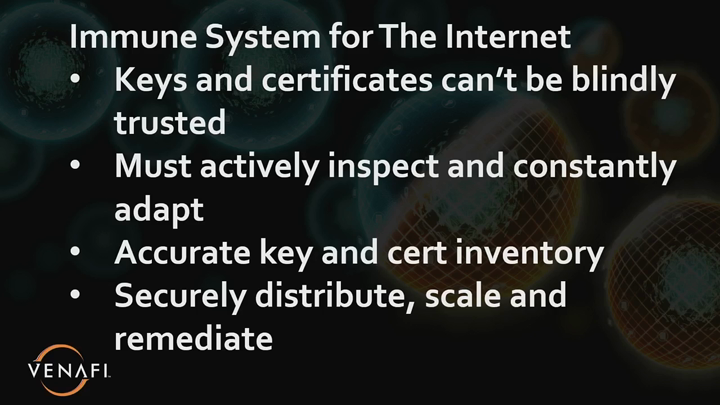
Along with DNS, digital keys and certificates are at the foundation of any layered cybersecurity defense. Moreover, keys and certificates are akin to HLAs (Human Leukocyte Antigens) because they serve as unique identifiers giving authorized users access to encrypted systems.
See Also: ISC2 & Gigamon Webinar: TLS 1.3: A New Private World
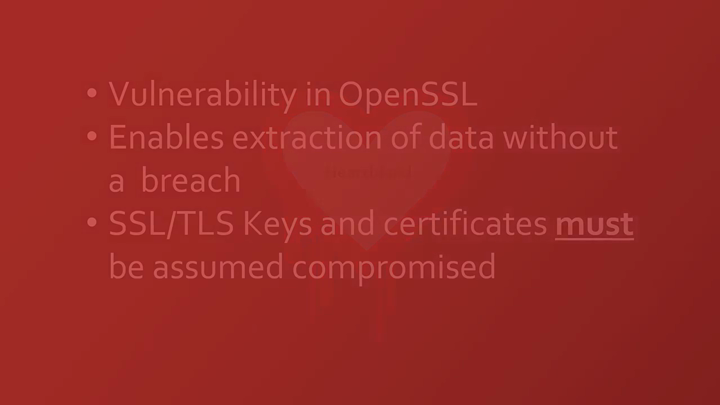
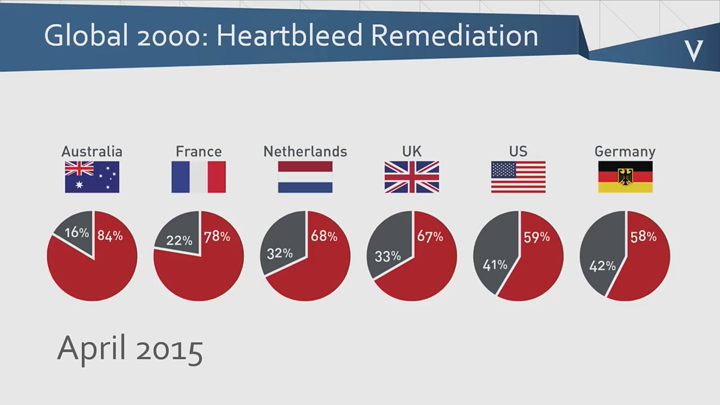
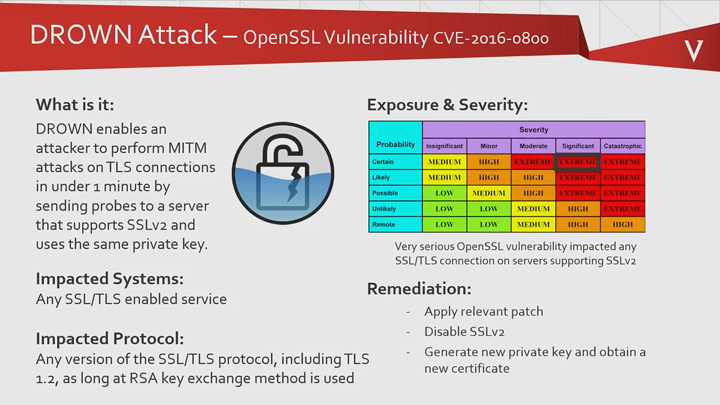
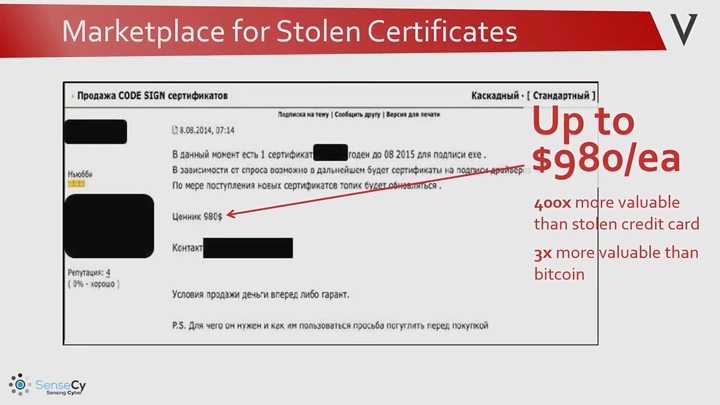
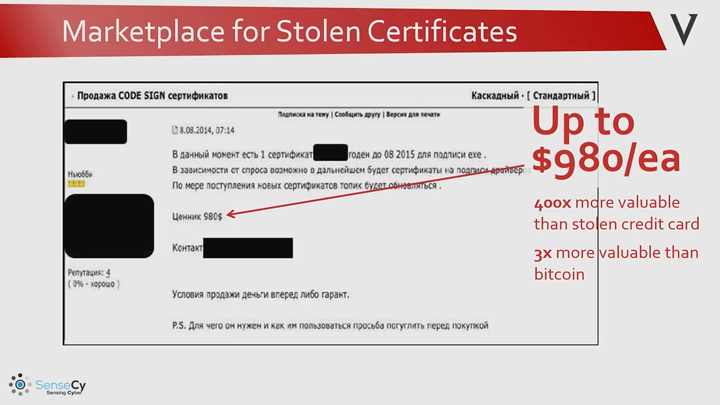
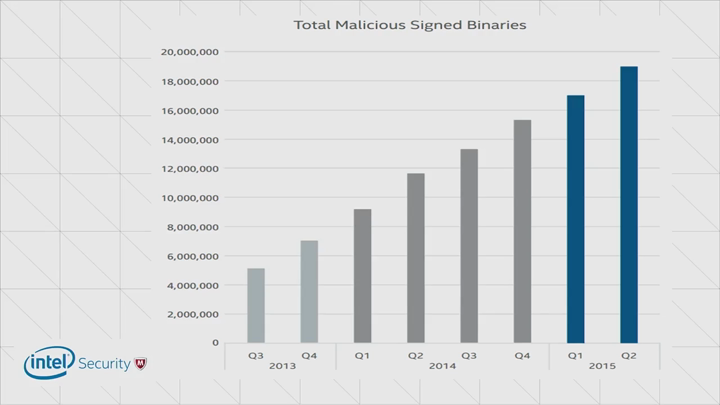
But vulnerabilities, such as Heartbleed and DROWN, are exploited to steal your digital keys and use them to infiltrate your systems - or sell them on the dark web for as much as $1,000 each? As the number of keys and certificates continue to increase (40 percent between 2013 and 2016 alone) and as more threat actors weaponize stolen keys and certificates, the need to immunize your system against complex, oftentimes overwhelming attacks is more important than ever before.
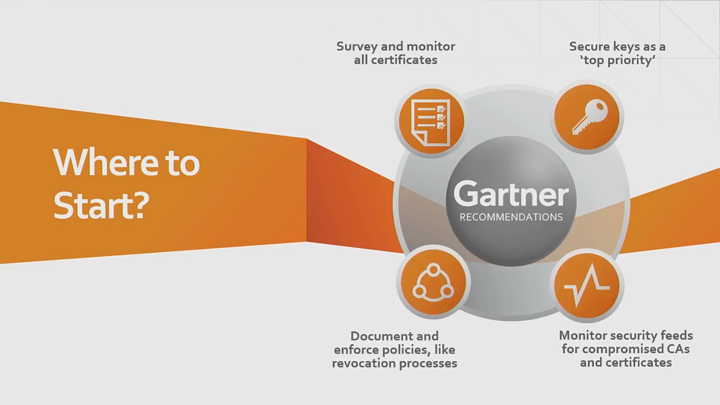
Join Mike Dodson of Venafi as he discusses:
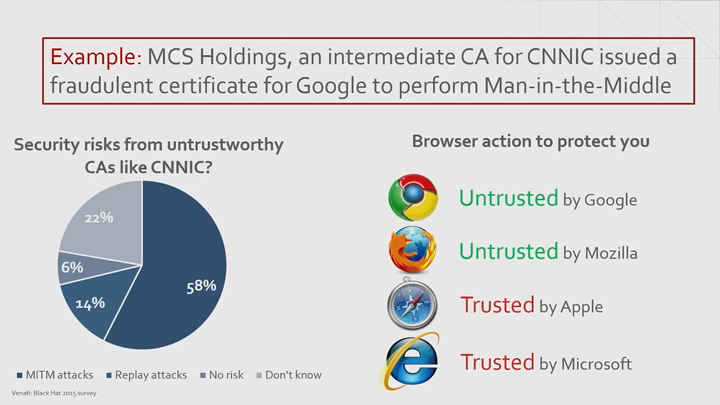
- Why 54 percent of organizations cannot determine whether digital keys are being misused;
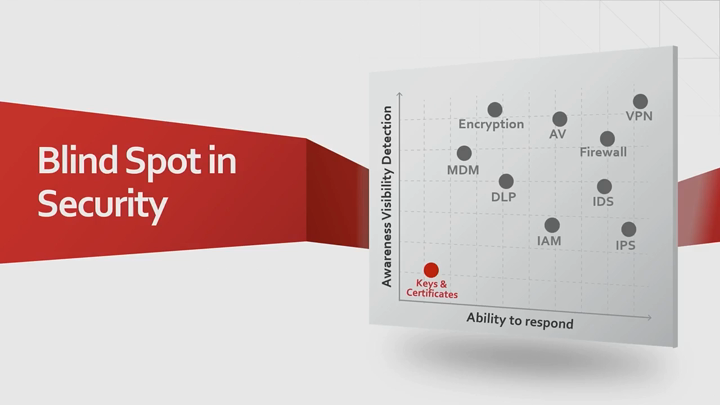
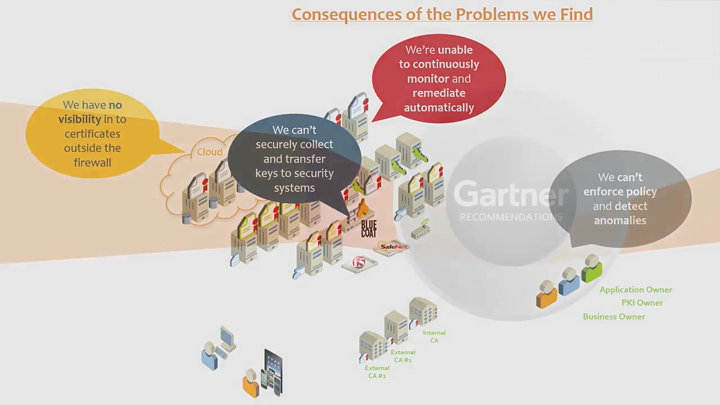
- Why organizations have a "blind spot" when trying to manage their keys and certificates; and
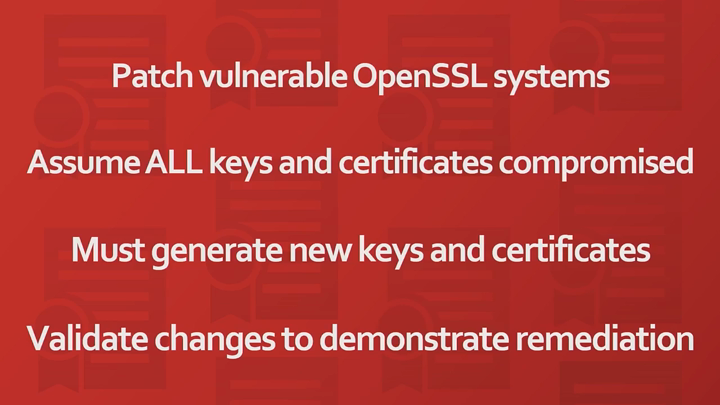
- Why you must assume that all of your SSL/TLS keys and certificates have been compromised - and how to fight back.
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.